How to self-host rybbit properly
"This website is being recorded for quality assurance purposes"
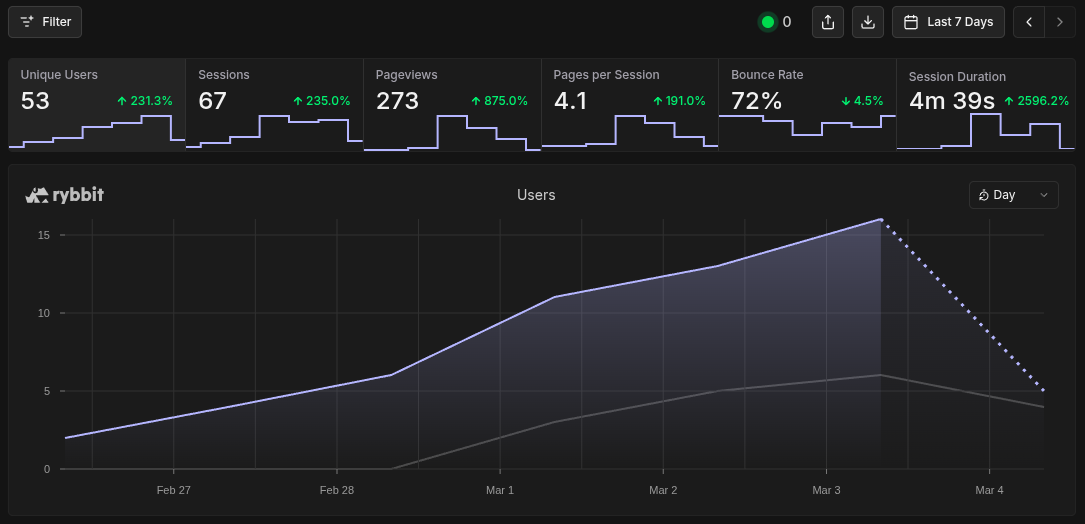
See the live analytics data from this website
Rybbit.io is a privacy respecting website analysis platform that is free and open source to anyone willing to run it on their platform.
At the moment, self hosting it gives you almost everything that the $13 a month tier does with the exception of the email related items (price list can be found here). It's exceptionally easy to get up and running, with a very intuitive and insightful display of information regarding how real users are interacting with your website. Since implementing rybbit on this site last week, I've seen traffic from 53 unique users from 11 different countries. Details you don't want to miss As I said above,...
Read more